Security professionals need to recognize what is new and adapt their security practices to accommodate. If not, virtualization will pose a significant security risk. Indeed, in recognition of these changes, independent 3rd party standards bodies, such as PCI and NIST, have modified their own regulations. Their updated specifications acknowledge that without appropriate technology and training, virtualization and cloud systems will introduce significant security and compliance gaps. Such gaps include unprotected networks, access control failures, loss of change controls, new threat surfaces, breakdowns in separation of duties and escalation of privilege. Virtualization security addresses these potential gaps while also reducing cost and complexity. While IT does need to update their own security practices and corporate governance in the face of virtualization, the net impact of virtualization on security can be extremely beneficial. Virtualization improves security by making it more fluid and context-aware. This means security is more accurate, easier to manage and less expensive to deploy than traditional physical security.
Security in a virtualized data center can also be more fully automated. Virtualization security gives data center administrators the power to automatically provision secure machines, automatically have security policies follow desktops when they move, automatically set up firewall rule sets for classes of servers and automatically quarantine compromised or out of compliance assets, amongst many examples. With the right technology and processes, virtualization has the power to make data centers even more secure and compliant than their physical counterparts.
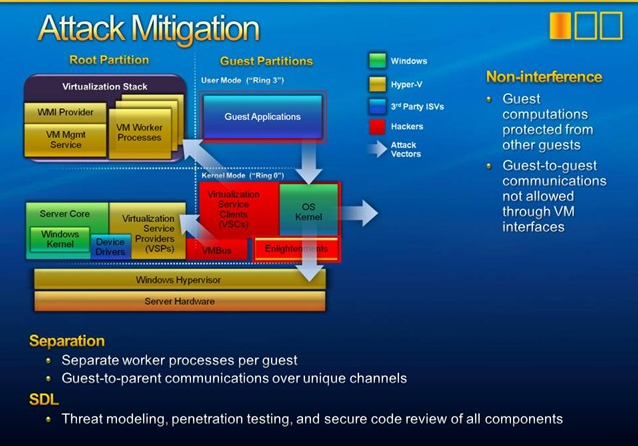
All virtualization platforms are not the same. Virtualization with Operations Management uses bare-metal virtualization, in which the hypervisor interfaces directly with computer hardware without the need for a host operating system. This approach safeguards Virtualization from OS-related vulnerabilities, making it the most robust and secure virtualization platform in the industry. The latest edition of Virtualization with Operations Management includes a range of innovations that enhance virtualization security even further. Bare-metal virtualization combined with other advanced capabilities makes the Virtualization platform exceptionally manageable and secure.
Small hypervisor footprint Simplifies deployment, maintenance and patching, and reduces vulnerability by presenting a much smaller attack surface. Software acceptance levels Prevents unauthorized software installation. Robust APIs Enable agentless monitoring, eliminating the need to install third-party software. Host firewall Protects the Virtualization host management interface with a configurable, stateless firewall. Improved logging and auditing Log all host activity under the logged-in user's account, making it easy to monitor and audit activity on the host. Secure syslog Log messages on local and/or remote log servers, with remote logging via either SSL or TCP connections. AD integration Configure the vSphere host to join an Active Directory domain; individuals requesting host access are automatically authenticated against the centralized user directory.
